Counterfeit Privacy Filter model reached top trending before takedown
A fake OpenAI repository on Hugging Face racked up ~244,000 downloads. It was trending on the platform before getting removed. The fake repo delivered a Rust stealer that pulled browser data, crypto wallets, and developer secrets on Windows computers.
Security researchers at HiddenLayer spotted the malicious repository under the namespace “Open-OSS/privacy-filter.” It was a typosquat of OpenAI’s genuine Privacy Filter model, which was released last month.
The fake listing copied OpenAI’s model card and tacked on instructions telling users to clone the repo and run the script.
Attackers used a fake OpenAI Privacy Filter
OpenAI’s real Privacy Filter is an open weight model that detects and redacts personally identifiable information in text.
The genuine release was under an Apache 2.0 license through both Hugging Face and GitHub. Developers expected to find runnable code and setup scripts in the real repo.
But attackers exploited developers’ expectations. They published a lookalike repository under a different namespace with familiar branding and almost identical documentation.
A Python file named loader, that looked like normal model loading code, had a fake DummyModel class and fake training output.
The script had a function that disabled SSL verification, decoded a secret URL, and received a command from JSON Keeper. JSON Keeper is a public JSON paste service. It lets the attacker swap payloads without interacting the repository.
The command started a hidden Windows PowerShell process. A batch script that imitates a blockchain analytics API, tried to increase privileges.
It tried to add Microsoft Defender exclusions for the payload directory. The comman then released the finished binary via a one time scheduled job that looked like a Microsoft Edge updater.
Next, a 1.07 MB Rust executable was delivered. It extracted browser data, Discord tokens, crypto wallet files, SSH, FTP, and VPN credentials. Stolen data got sent to a command-and-control (C2) server.
The malware also evaded virtual machines, sandboxes, and debuggers in case researchers setup an automated analysis.
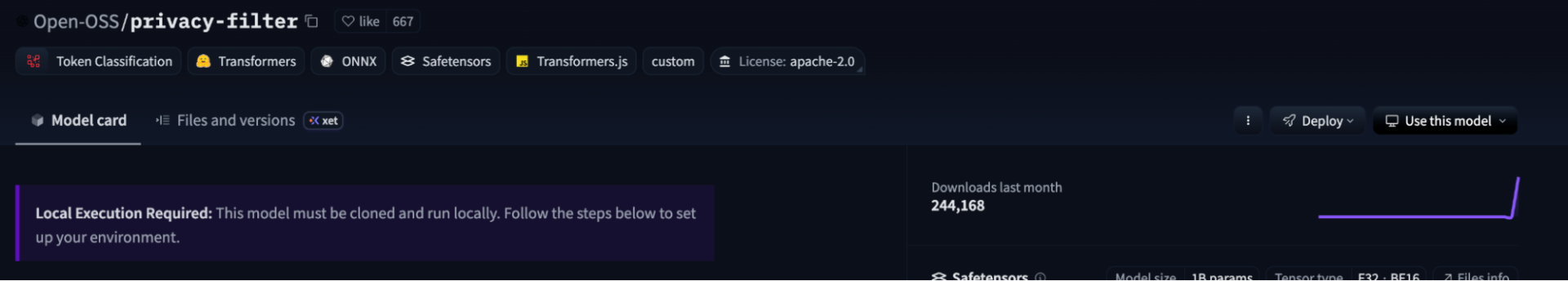 A screenshot of the fake OpenAI repository. Source: HiddenLayer.
A screenshot of the fake OpenAI repository. Source: HiddenLayer.
The 244,000 downloads does not mean confirmed infections. Its unknown how many users executed the malicious files.
Neither OpenAI nor Hugging Face had issued a public statement. The available evidence points to platform impersonation only. There’s no compromise of either OpenAI or Hugging Face.
OpenAI’s Privacy Filter launch generated search traffic from developers.
Steps for anyone who cloned the repo
Anyone who cloned the repository and ran the malicious scripts should consider their Windows machin compromised. Reimaging the machine is only effective solution in removing the malacious files.
Logging into any account on the affected machine risks further exposure. Security researchers recommend rotating every credential stored in browsers, password managers, or credential stores on the device. That includes saved passwords, session cookies, OAuth tokens, SSH keys, and cloud provider tokens.
Crypto funds should be moved to a new wallet created on a healthy device.
In March, security researchers identified a malicious npm package disguised as an installer for the AI tool OpenClaw. It targeted system passwords and crypto wallets. That package, named GhostLoader, installed itself as a hidden telemetry service and scanned for AI agent credential stores.
If you're reading this, you’re already ahead. Stay there with our newsletter.
You May Also Like

New CLARITY Act Text Is Out: Expert Claims XRP Looks Strong In The Details

Iran invites global powers to negotiate Strait of Hormuz transit






