Kaspersky flags new crypto malware targeting seed phrase screenshots
A new strain of mobile spyware is targeting crypto users by stealing screenshots of their wallet seed phrases, with some infected apps slipping past Apple and Google’s store defenses.
Kaspersky has uncovered a new strain of mobile crypto malware that targets screenshots of seed phrases from crypto users’ phone photo galleries. The malware was spreading through both Android and iOS apps, some of which made it onto official app stores, including Google Play and Apple’s App Store.
Targeting primarily users in Southeast Asia and China, the new malware dubbed SparkKitty appears to be a relative of SparkCat, a previous malware campaign discovered in January. Like SparkCat, this new variant focuses on stealing photos containing sensitive information.
The malware is hidden inside seemingly legitimate apps, including TikTok mods, crypto trackers, gambling games, and adult content apps. These apps trick users into installing a special developer profile, which allows the malware to run outside of the phone’s usual app review protections.
Once installed, the malware waits until the user opens specific screens (e.g. a support chats) and then asks for access to the photo gallery. If granted, it quietly scans images using optical character recognition to identify and steal screenshots containing text.
Many of the fake apps had strong crypto themes, and several included crypto-only stores, suggesting that seed phrase collection was the goal.
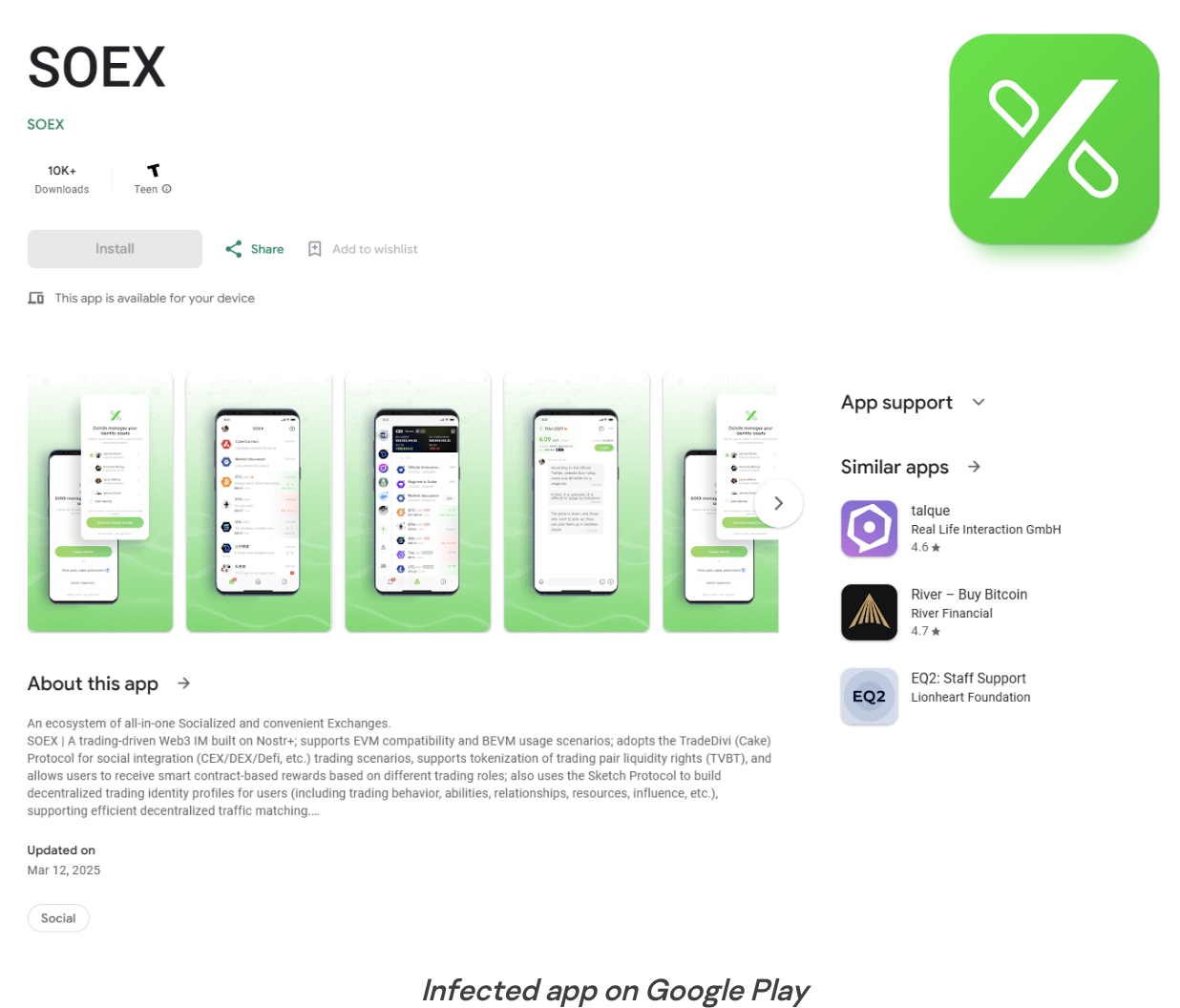
For example, two apps flagged in the reports were Soex Wallet Tracker and Coin Wallet Pro. Soex, which posed as a portfolio manager with real-time tracking features, was downloaded over 5,000 times from Google Play before it was pulled.
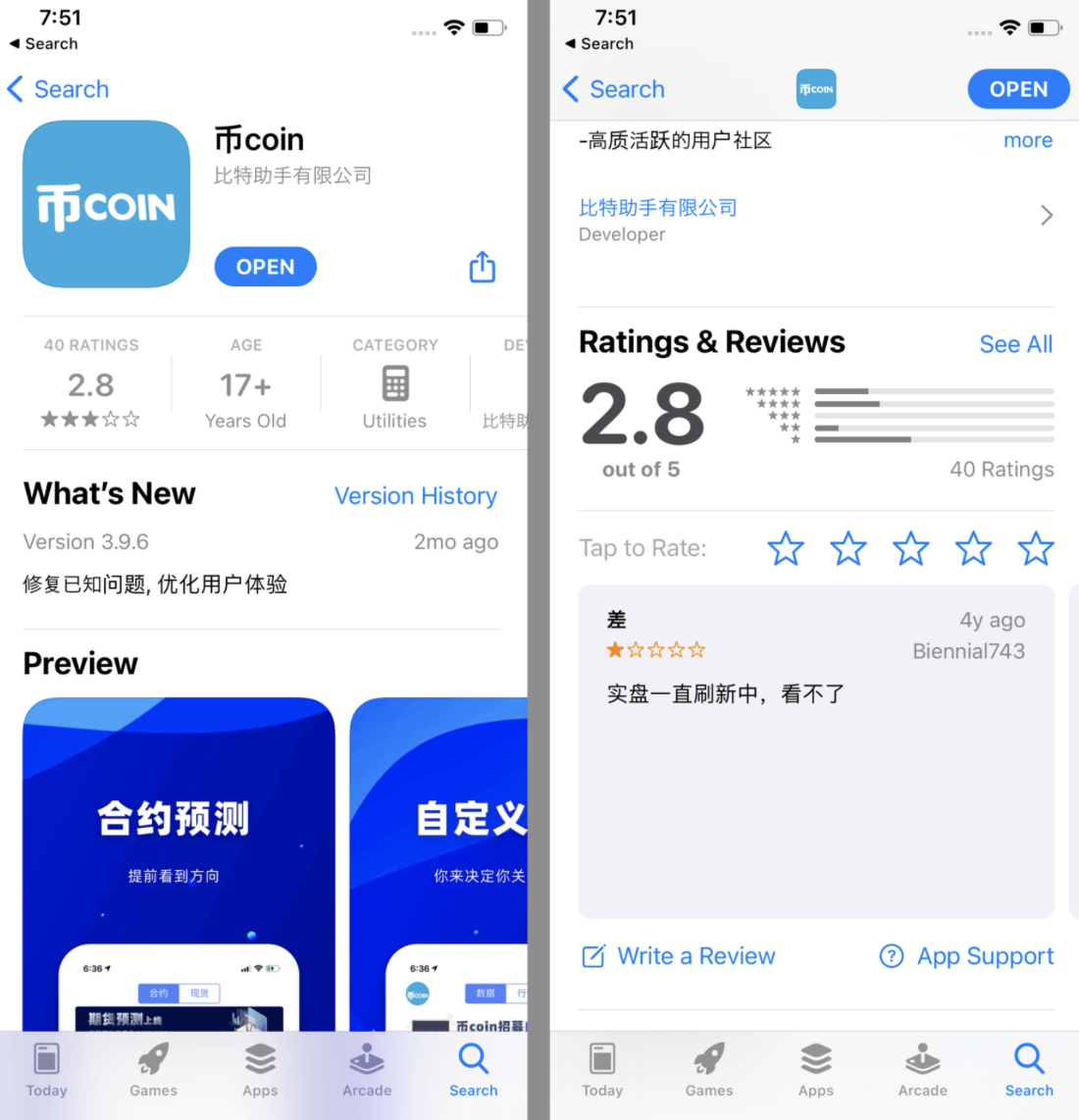
Coin Wallet Pro, which marketed itself as a secure multi-chain wallet, appeared briefly on the App Store, gaining traction through social media ads and Telegram promotions before its removal.
Kaspersky has notified both Apple and Google, and the affected apps have since been removed from their stores. The researchers said the campaign had been running since at least April 2024, with some samples dating back even earlier.
You May Also Like

Wall Street’s Tokenisation Boom Runs Into Infrastructure Challenges

Zcash (ZEC) Rockets 1,200%—Expert Says ZEC Could Soon Outgrow Cardano (ADA)






