Beware: New ‘DeadLock’ Ransomware Weaponizes Polygon Smart Contracts to Stay Invisible
Cybersecurity researchers are becoming interested in a newly discovered ransomware strain called DeadLock that abuses Polygon smart contracts to silently service its infrastructure and bypass conventional detection tools, as a recent report by threat intelligence firm Group-IB depicts.
DeadLock, first observed in July 2025, has so far remained largely under the radar because it does not have a publicly facing affiliate program, it does not have a data leak site, and its victims have been connected to comparatively few confirmed victims.
That profile, however, covers a more technologically sophisticated strategy that researchers believe is showing a more global change in the way cybercriminals are using public blockchains for criminal ends.
How DeadLock Hides Ransomware Infrastructure Inside Polygon Smart Contracts
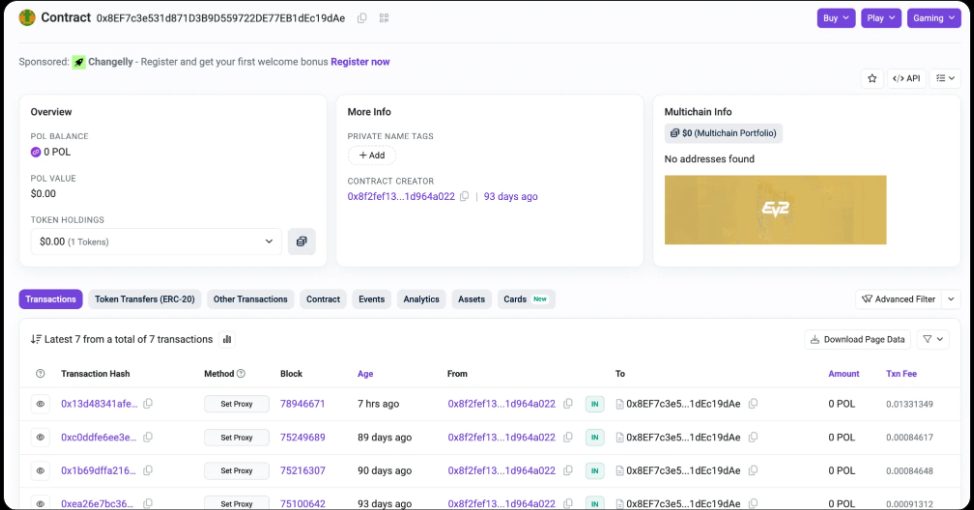
Group-IB’s analysis shows that DeadLock uses smart contracts deployed on the Polygon network to store and rotate proxy server addresses.
These proxies act as intermediaries between infected systems and the ransomware operators, allowing command-and-control traffic to shift endpoints without relying on centralized infrastructure that can be seized or blocked.
By querying the smart contract, the malware retrieves the current proxy address through a simple read operation that leaves no obvious transactional footprint and incurs no network cost.
Researchers said this technique mirrors earlier campaigns, such as EtherHiding, disclosed last year, in which North Korean threat actors used the Ethereum blockchain to conceal and distribute malware payloads.
In both cases, public and decentralized ledgers were turned into resilient communication channels that are difficult for defenders to disrupt. DeadLock’s use of Polygon extends that concept by embedding proxy management directly into a smart contract, allowing attackers to update infrastructure on demand.
 Source: Group-IB
Source: Group-IB
Once deployed, DeadLock encrypts files and appends a “.dlock” extension, alters system icons, and replaces the victim’s wallpaper with ransom instructions.
Over time, the group’s ransom notes have evolved, with early samples referencing only file encryption, while later versions explicitly stated that sensitive data had been stolen and threatened its sale if payment was not made.
The most recent ransom notes also promise “added services,” including a breakdown of how the network was breached and assurances that the victim will not be targeted again.
This Ransomware Doesn’t Just Lock Files — It Opens a Chat With Hackers
Group-IB identified at least three distinct DeadLock samples from mid-2025, each showing incremental changes in tactics.
Analysis of associated PowerShell scripts suggests the malware aggressively disables non-essential services, deletes volume shadow copies to prevent recovery, and whitelists a limited set of processes, notably including AnyDesk
Investigators believe AnyDesk is used as the primary remote access tool during attacks, a finding consistent with separate digital forensics investigations.
A key element of DeadLock’s operation is an HTML file dropped on infected systems that embeds an encrypted session messenger interface. Victims can communicate directly with attackers through this file without installing additional software.
The embedded JavaScript retrieves proxy addresses from the Polygon smart contract, then routes encrypted messages through those servers to a session ID controlled by the ransomware operators.
Transaction analysis shows that the same wallet created multiple identical smart contracts and repeatedly updated proxy addresses by calling a function labeled “setProxy.”
The wallet was funded through an exchange-linked address shortly before the contracts were deployed, indicating deliberate preparation.
Historical tracking of these transactions allows defenders to reconstruct past proxy infrastructure, although the decentralized design complicates rapid takedown efforts.
The finding is part of an overall increase in crypto-related cybercrime, as over $3.4 billion was stolen by hacks and exploits as of early December 2025, with state-linked North Korean groups accounting for over $2 billion of that total.
You May Also Like

Pi Network Supply Shock Could Reshape Long Term Pi Coin Value Structure

Fed holds rates steady amid rising inflation, US-Iran tensions






