Ubuntu Vulnerability Signals Rising CX Risks in Digital Infrastructure
Security Vulnerability in Ubuntu Highlights Hidden Risks to Digital Customer Experience
A newly identified vulnerability in Ubuntu is drawing attention to a critical yet often overlooked dimension of customer experience: the resilience and security of underlying infrastructure.
Qualys Threat Research Unit has disclosed CVE-2026-3888, a flaw affecting default installations of Ubuntu Desktop 24.04 and later. The vulnerability enables a local, unprivileged user to escalate privileges to root access by exploiting interactions between two standard system components—snap-confine and systemd-tmpfiles. While exploitation requires specific timing conditions, the potential outcome is a full system compromise.
The finding highlights a broader issue in modern digital environments: risks that emerge not from isolated flaws, but from the interaction of trusted components.
Infrastructure Reliability as a CX Imperative
Customer experience is increasingly shaped by the performance and reliability of complex digital ecosystems. Organizations today deliver services through interconnected platforms that rely on cloud infrastructure, open-source software, and continuous deployment pipelines.
In this environment, customers expect seamless, always-on interactions. Service interruptions, security breaches, or degraded performance are no longer tolerated and can quickly erode trust.
Open-source operating systems such as Ubuntu play a foundational role in powering digital services—from enterprise applications to customer-facing platforms. Their flexibility and scalability make them essential to digital transformation initiatives.
However, their widespread use also makes them critical points of vulnerability. The issue identified by Qualys illustrates how routine system processes—such as temporary file management—can introduce risk when combined in unexpected ways.
For CX leaders, this reinforces the need to view infrastructure not just as an IT asset, but as a core component of experience delivery.
Qualys’ Strategic Positioning in Proactive Security
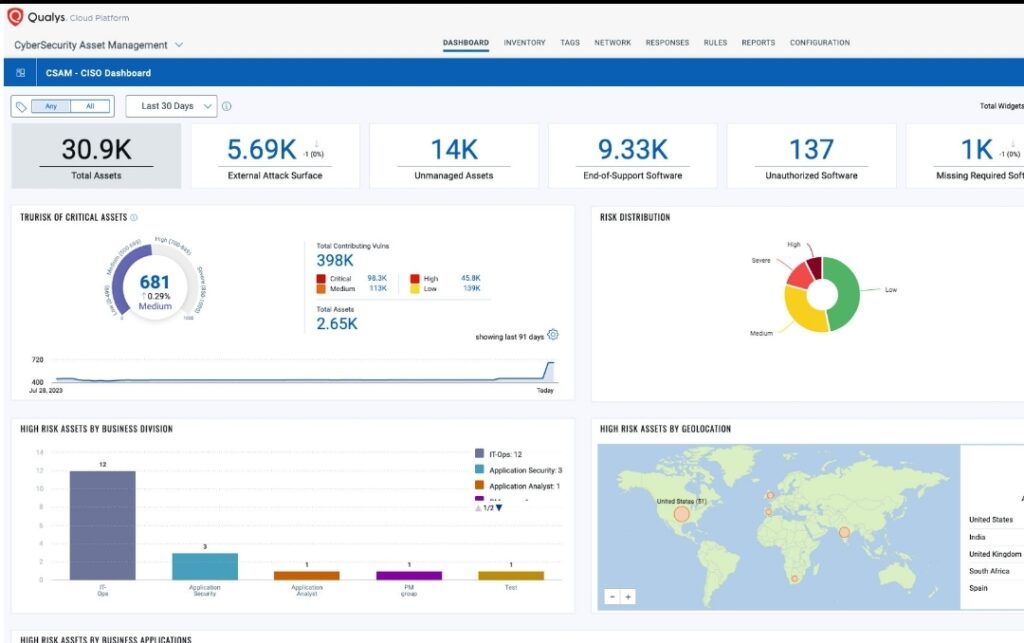
Qualys continues to strengthen its position as a provider of continuous security intelligence. The discovery of CVE-2026-3888 aligns with its broader focus on proactive vulnerability detection and real-time risk visibility.
By identifying a flaw rooted in component interaction, rather than a single-point weakness, Qualys demonstrates a deeper level of threat research. This approach reflects the evolving nature of cybersecurity, where risks increasingly arise from system complexity.
The introduction of a dedicated detection identifier (QID 386810) further supports a platform-driven strategy. It enables organizations to quickly identify exposure and take corrective action within existing workflows.
From a business perspective, this reinforces Qualys’ role in helping enterprises maintain secure and stable environments—an essential requirement for delivering consistent customer experiences.
Understanding the Technical Dynamics
The vulnerability stems from the interaction between snap-confine and systemd-tmpfiles—two standard components within Ubuntu environments.
Snap-confine is part of the Snap ecosystem, responsible for managing application execution and confinement. Systemd-tmpfiles, on the other hand, handles the creation and cleanup of temporary directories.
Under certain conditions, the management of these temporary directories can be manipulated. An attacker can exploit this behavior to influence file system operations performed by snap-confine, ultimately gaining unauthorized access to privileged resources.
Because the exploit does not require administrative privileges, it presents a significant risk in multi-user environments. Over time, and within a specific time window, an attacker can escalate privileges to full root access.
This type of vulnerability underscores a critical challenge: ensuring security not just at the component level, but across the interactions that define modern systems.
CX Implications: From Backend Risk to Frontend Impact
Although the vulnerability exists deep within the system architecture, its impact can extend directly to customer-facing experiences.
A compromised system can lead to outages, service degradation, or unauthorized data access. For customers, this may appear as failed transactions, slower response times, or concerns about data integrity.
In sectors such as e-commerce, financial services, and SaaS, these disruptions can have immediate consequences—ranging from lost revenue to reputational damage.
Proactive vulnerability detection and timely patching help mitigate these risks before they affect users. This reduces operational friction, minimizes downtime, and ensures continuity of service.
Security also plays a key role in building trust. Customers may not see the underlying systems, but they experience their reliability. Consistent performance and data protection are essential to maintaining confidence in digital interactions.
Broader Industry Implications
The discovery of CVE-2026-3888 reflects a broader shift in how organizations must approach cybersecurity.
As technology ecosystems become more modular, vulnerabilities are increasingly emerging from the interaction between components rather than from individual flaws. This requires a more holistic approach to security—one that considers the entire system lifecycle.
Enterprises are responding by investing in continuous monitoring, automated detection tools, and integrated security platforms. There is also a growing emphasis on zero-trust architectures and faster patch management cycles.
From a competitive standpoint, organizations that can ensure higher levels of system resilience will be better positioned to deliver reliable customer experiences and build long-term trust.
Future Outlook: Security as a Foundation of CX
The intersection of cybersecurity and customer experience is becoming more pronounced as digital transformation accelerates.
Organizations are no longer able to treat security as a back-office function. Instead, it must be embedded into the design and operation of customer experiences.
Incidents like this highlight the importance of anticipating risks before they materialize. Preventing disruptions is increasingly as important as responding to them.
Looking ahead, CX leaders will need to work more closely with IT and security teams to ensure that infrastructure resilience supports business objectives. This includes integrating security metrics into CX measurement frameworks and aligning technology investments with experience outcomes.
In an environment where trust is a key differentiator, the ability to deliver secure, reliable experiences will define competitive advantage.
Key Takeaways
- Critical Ubuntu vulnerability enables full system compromise
The flaw in Ubuntu allows local users to escalate privileges to root access, creating significant risk for enterprise environments, especially those with multiple users. - System interactions are emerging as a major security risk
The issue identified by Qualys Threat Research Unit highlights how vulnerabilities can arise from the interaction between trusted components—not just standalone weaknesses. - Infrastructure security directly impacts customer experience
Backend vulnerabilities can lead to outages, degraded performance, or data risks, all of which affect customer trust and service continuity. - Proactive detection and patching are critical for CX resilience
Early identification, supported by solutions from Qualys, enables organizations to mitigate risks before they disrupt customer journeys. - Security is becoming a competitive differentiator in CX
Organizations that ensure stable, secure digital environments are better positioned to deliver consistent experiences and build long-term customer trust.
The post Ubuntu Vulnerability Signals Rising CX Risks in Digital Infrastructure appeared first on CX Quest.
You May Also Like

CEO Sandeep Nailwal Shared Highlights About RWA on Polygon

Velo protocol Integrates SumPlus to Power AI-Driven Finance