Fake “Red Alert” App Campaign: CX Lessons from Crisis-Driven Malware Exploitation
When Panic Becomes a Payload: What CX Leaders Must Learn from the Fake “Red Alert” App Campaign
Imagine this.
Your phone buzzes at 2:17 a.m.
A message claims to be an urgent update to a life-saving emergency app.
You click. You install. Plus, you trust.
Now imagine your customers doing the same.
That is the real story behind the latest threat uncovered by . The company has identified a malicious Android campaign spreading a fake version of Israel’s “Red Alert” emergency app. The legitimate app is operated by . The fake version impersonates it convincingly.
The result? Stolen SMS data, contact lists, and precise location information. All harvested under the cover of urgency and public safety.
For CX and EX leaders, this is not just a cybersecurity headline. It is a masterclass in trust breakdown, journey fragmentation, and crisis exploitation.
Let’s unpack what happened and what it means for customer experience strategy.
What Happened in the Fake “Red Alert” App Campaign?
In short: attackers exploited crisis-driven urgency to distribute a trojanized Android app through SMS spoofing.
According to CloudSEK’s threat intelligence report, attackers distributed a fake APK that mimicked Israel’s official “Red Alert” emergency warning app. The campaign emerged amid the ongoing Israel-Iran conflict, when public demand for real-time alerts spiked.
The malicious app:
- Closely replicated the user interface of the legitimate app
- Requested high-risk permissions during onboarding
- Harvested SMS data, contacts, and precise location
- Exfiltrated data to attacker-controlled infrastructure
It even continued delivering alert-style functionality to maintain credibility.
That detail is critical.
The malware did not just attack. It sustained the illusion of value.
Why Should CX and EX Leaders Care?
Because this campaign weaponizes the very pillars of modern customer experience: trust, urgency, and digital dependency.
Today’s CX ecosystems rely on:
- Real-time notifications
- SMS-based engagement
- App-driven journeys
- Crisis communication platforms
Attackers exploited all four.
If your organization operates in fintech, healthcare, telecom, public services, or retail, you use similar engagement mechanics. Your customers are trained to respond quickly to alerts.
The difference between engagement and exploitation is now razor thin.
How Did the Attack Technically Work?
The malware used advanced evasion techniques to bypass basic security checks.
CloudSEK’s technical analysis identified:
- Signature spoofing
- Installer spoofing
- Reflection-based obfuscation
- Multi-stage payload loading
Once active, the app harvested sensitive data and sent it to endpoints such as api[.]ra-backup[.]com/analytics/submit.php.
In a conflict environment, this has implications beyond fraud.
Location data could map shelter activity.
SMS interception could expose operational messages.
Contact lists could enable targeted phishing waves.
This becomes physical security risk, not just digital compromise.
As Shobhit Mishra, Threat Intelligence Researcher at CloudSEK, stated:
That statement should resonate deeply with CX leaders.
What Is Crisis Exploitation and Why CX Teams Must Understand It?
Crisis exploitation is the strategic use of fear and urgency to manipulate digital behavior at scale.
Modern customers live inside notification ecosystems. In emergencies, they suspend skepticism. They act quickly. They trust authority signals.
Attackers know this.
For CX teams, crisis moments create three vulnerabilities:
- Acceleration of decision-making
- Reduced verification behavior
- Higher dependency on digital touchpoints
Your journey maps rarely account for malicious interception of trust.
They should.
How Does This Connect to Journey Fragmentation?
Journey fragmentation occurs when customers move across channels without consistent verification or context.
This campaign exploited fragmentation in three ways:
1. SMS as an Entry Point
The attackers used spoofed SMS messages to drive installation. SMS remains one of the most trusted channels globally.
Yet many CX leaders treat SMS as a pure engagement tool, not a security surface.
2. Sideloaded App Journeys
The malicious APK was distributed outside official app stores. Many organizations do not educate customers about sideloading risks.
If your customers install updates from links, you have a vulnerability gap.
3. Onboarding Permission Blindness
The fake app aggressively requested permissions. The legitimate version did not.
Yet most users do not compare permission scopes. They click “Allow.”
That is a UX design and digital literacy challenge.
What Strategic Patterns Does This Reveal?
CloudSEK’s findings underscore a broader pattern: attackers increasingly weaponize real-world crises and trusted institutions.
This pattern includes:
- Impersonation of public safety platforms
- Exploitation of geopolitical tension
- Leveraging high-volume notification channels
- Embedding malware inside functional-looking apps
This is emotional engineering at scale.
CX strategy must now incorporate adversarial thinking.
What Framework Can CX Leaders Use to Build Digital Resilience?
Here is a practical framework for experience-driven security alignment.
The TRUST-LENS Model
T – Threat Modeling Inside Journeys
Map where attackers could impersonate your brand.
R – Real-Time Channel Governance
Audit SMS, email, push, and WhatsApp flows for spoofing risk.
U – User Education Nudges
Embed micro-copy that teaches safe download behavior.
S – Store-Only Distribution Enforcement
Discourage sideloading through app design and messaging.
T – Transparency During Crises
Communicate official channels clearly during high-risk periods.
L – Least Privilege by Default
Limit app permissions aggressively.
E – External Intelligence Integration
Partner with predictive threat platforms like CloudSEK.
N – Notification Authentication Standards
Adopt cryptographic verification and visible trust markers.
S – Security-CX Governance Council
Break silos between security, CX, product, and communications.
This model aligns experience design with proactive threat intelligence.
What Are the Common Pitfalls CX Teams Must Avoid?
Pitfall 1: Treating Security as IT’s Problem
Security is a trust issue. Trust is a CX issue.
Pitfall 2: Overloading Users with Permissions
Every permission request erodes credibility.
Pitfall 3: Ignoring Crisis Playbooks
Crisis moments amplify attack success rates.
Pitfall 4: No Real-Time Threat Feeds
Without predictive intelligence, your CX roadmap lags behind attackers.
Key Insights for CX and EX Leaders
- Urgency is a vulnerability multiplier.
- Impersonation attacks now mimic functional value.
- Location data theft can become physical risk.
- Crisis communications require hardened design.
- Siloed teams create blind spots attackers exploit.
Security posture now defines brand perception.
How Should Organizations Operationalize This?
Move from reactive alerts to predictive governance.
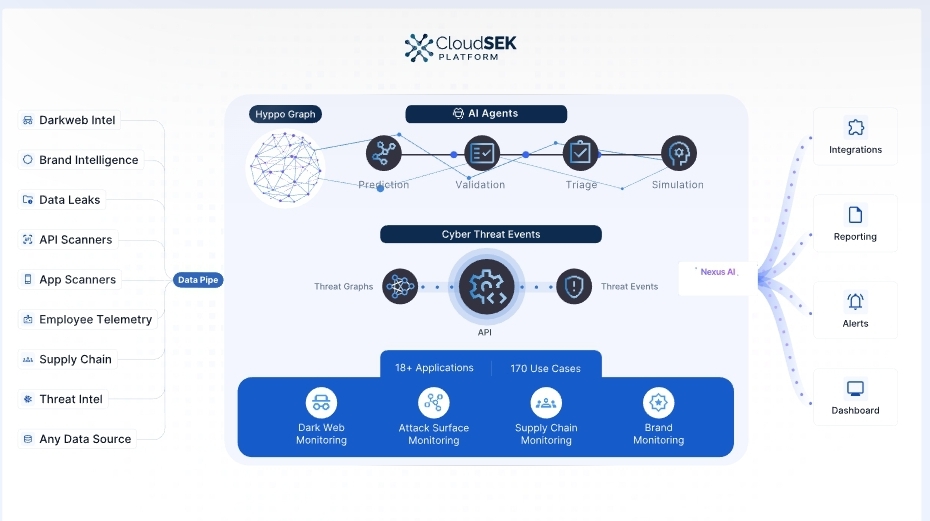
CloudSEK positions itself as a predictive cyber threat intelligence platform. Its cloud-native SaaS model continuously maps digital footprints and identifies emerging attack paths.
For CX leaders, this means:
- Integrating threat intelligence into journey analytics
- Monitoring dark web chatter around brand impersonation
- Tracking spoofed domains and APK variants
- Proactively blocking indicators of compromise
Digital experience metrics must now include trust-risk indicators.
FAQ: What CX Leaders Are Asking
How can CX teams detect impersonation risks early?
Partner with threat intelligence providers and monitor spoofed domains, APK variants, and SMS phishing trends.
Why are emergency apps especially attractive to attackers?
They create urgency, reduce skepticism, and justify high-risk permissions.
Should CX teams own customer security education?
Yes. Security literacy improves experience quality and brand trust.
How do we reduce sideloading risk?
Promote official app store links only. Add in-app warnings about unofficial updates.
Can predictive intelligence improve CX outcomes?
Yes. It reduces breach-related churn and preserves trust equity.
Actionable Takeaways for CX Professionals
- Map high-risk crisis scenarios in your journey architecture.
- Audit all SMS and push notification flows for spoofing exposure.
- Align security and CX leaders in a monthly governance forum.
- Embed permission transparency messaging in onboarding UX.
- Promote official distribution channels aggressively during crisis periods.
- Adopt predictive threat intelligence monitoring for brand impersonation.
- Track trust metrics alongside NPS and CSAT.
- Create crisis-specific communication playbooks with verified digital signatures.
The fake “Red Alert” campaign is not just malware news.
It is a warning about the future of digital trust.
In a world where panic becomes payload, CX leaders must design not just for delight, but for defense.
Because when customers click in fear, your brand carries the consequence.
The post Fake “Red Alert” App Campaign: CX Lessons from Crisis-Driven Malware Exploitation appeared first on CX Quest.
Ayrıca Şunları da Beğenebilirsiniz

Why Bitcoin Needed A Remodel With Segwit And Taproot

XRP Whales Accumulated 1.3 Billion XRP In Just 48 Hours. What’s Happening?
